by Marco Tiggelaar | Jan 30, 2015 | Future-Proof Business IT
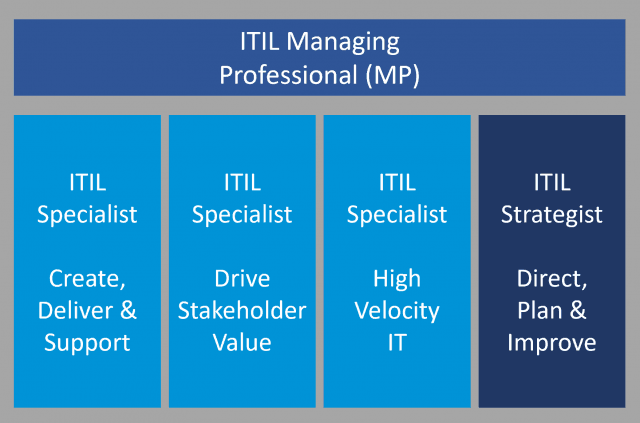
If you are a big company that has the financial resources to maintain a full-blown IT department, you have probably been implementing the best practices documented in the information technology infrastructure library (ITIL), and this post may have little relevance for...

by Marco Tiggelaar | Jan 25, 2015 | Networking & Infrastructure
Does your network run mainly on a Linux server? Just like any other network server, your Linux system needs to be checked regularly to keep it in good shape. There are a few things you may be able to do without having to call for outside help. One of the most...

by Marco Tiggelaar | Jan 17, 2015 | Networking & Infrastructure
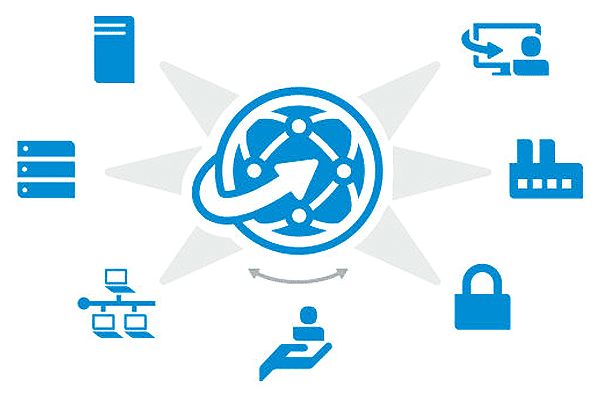
Infrastructure, in the context of IT servers, is simply organized server support. It refers to how the servers are physically, logically, and/or functionally grouped together and includes the tools (mostly provided by vendors and occasionally custom-made by the system...

by Marco Tiggelaar | Jan 12, 2015 | Future-Proof Business IT
The idea of converged infrastructure revolves around forming a single optimized IT package by putting together several components to meet present-day business needs. According to HP, converged infrastructure meets these needs “by bringing storage, servers, networking,...

by Marco Tiggelaar | Dec 29, 2014 | Cybersecurity & Compliance
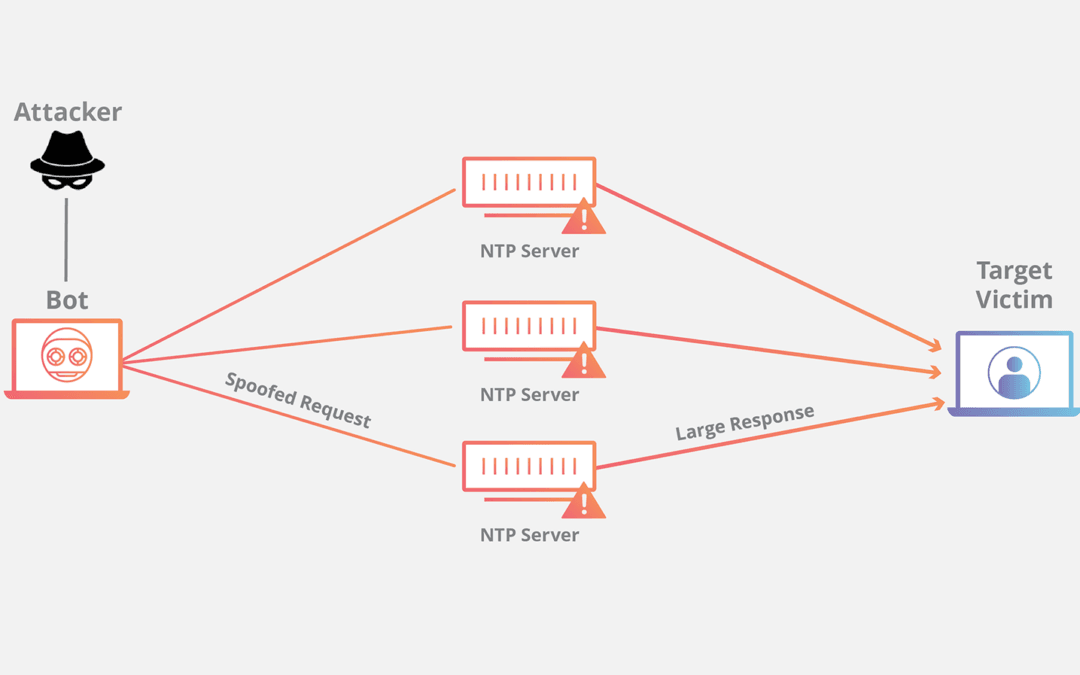
At least three serious vulnerabilities in the Network Time Protocol (NTP) have been uncovered by security researchers at Google in 2014. This is quite serious because of the sheer number of computers that may potentially be targets of DDoS (click here to read earlier...